Data Breaches
Privacy Rights Clearinghouse brings together publicly reported data breach notifications from across U.S. government agencies into a single, searchable database. Explore our interactive visualizations or purchase the full dataset. Have questions? Check our FAQ below.
Explore the Data Breach Chronology
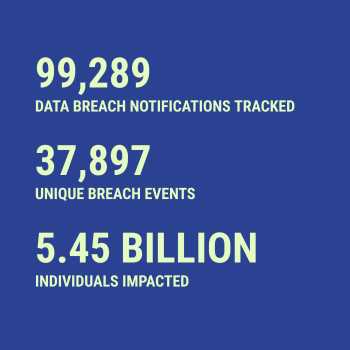
Nearly 100,000 reported data breaches since 2005, at your fingertips. Search by organization, breach type, state, or data source to view individual incidents and track broader trends.
Tracking Two Decades of Data Breaches in the U.S.
Data breaches have exposed the personal information of hundreds of millions of people across the U.S., affecting individuals, businesses, and entire industries - and in many cases many times over. The Data Breach Chronology compiles more than 75,000 reported breaches since 2005 using publicly available notifications exclusively from government sources. While reporting requirements vary by state and disclosure practices differ, this database offers the most comprehensive view available of who was breached, how it happened, and what data was compromised. It captures breach types, along with affected organizations, compromised information, and reporting timelines. By downloading the database, you gain structured, standardized access to fragmented public records, enabling research, risk analysis, policy development, and investigative reporting based on the best data currently available.
Power Your Research With the Data Breach Chronology
You can download the database and support this project with your purchase.
Try a sample in your preferred format:
- Download SQLite sample (.db file, recommended)
- Download Excel sample (.xlsx file)
- Download CSV sample (.csv file)
See our README for documentation.
We offer flexible pricing options for individual researchers and organizations, with substantial academic discounts. Choose from individual researcher access for personal projects, or a multi-user license for classroom and organisational access for teams. Annual subscriptions include ongoing access to monthly database updates and new features.
If you're conducting academic research with limited institutional funding, working with a nonprofit, or are a media outlet operating on a limited budget, and your work directly advances privacy protection, we offer limited complimentary access. Please contact us at databreachchronology@privacyrights.org with detailed information about your funding situation, research project, and how your work aligns with our mission of advancing consumer privacy protections. We typically respond within 3-5 business days.